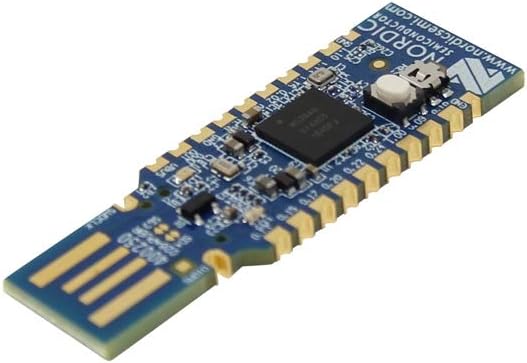
Device Instance Path
USB\VID_1915&PID_520C&MI_00\6&20A3E423
VendorID
1915
ProductID
520C
Class
USB
Author
@enesilhaydin
Sigma/Yara Rules
Coming Soon…
Links
1- https://www.amazon.com.tr/Nordic-nRF52840-Dongle-Bluetooth-Zigbee/dp/B07MCYTZ2S
2- https://medium.com/@enesilhaydin/mini-mini-logitech-rubber-ducky-6016c72916eb